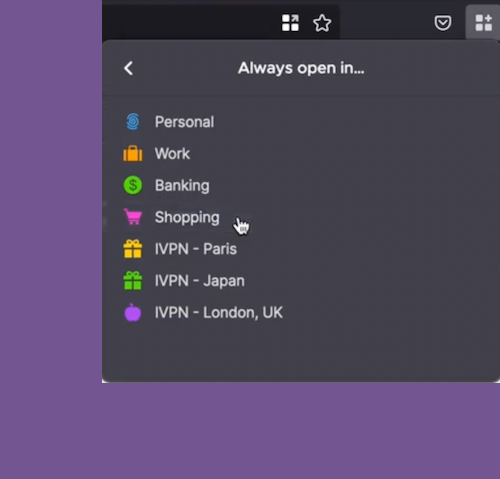
Better tracker blocking controls with AntiTracker Plus
IVPN AntiTracker is an optional feature of the VPN service that improves privacy protection by blocking requests from unwanted trackers and ads. Before today, AntiTracker operated with one blocklist option - OISD Big. With AntiTracker Plus we introduce ten different blocklist options to choose from:
Continue reading